BloodHound
What is Bloodhound?
BloodHound is an Active Directory reconnaissance tool that uses graph theory to reveal hidden relationships and attack paths (ACLs, Group memberships, Trusts) within an AD environment.
Setup
C:\AD\Tools\neo4j-community-4.4.5-windows\bin\neo4j.bat console
C:\AD\Tools\BloodHound-win32-x64\BloodHound.exe
sudo docker-compose up -d
sudo docker compose logs bloodhound | grep "Initial Password Set" -A 2
http://localhost:8080
sudo neo4j console
bloodhound
Recollect Data
. C:\AD\Tools\SharpHound.ps1
# Full data collection (ACLs, Groups, Trusts)
# NOTE: Avoid in production/exams due to high noise (MDI triggers).
Invoke-BloodHound -CollectionMethod All
# Only session data (Minimizes network noise; skips bulk ACL/GPO queries)
Invoke-BloodHound -Stealth
# Skips session enumeration on DCs (Avoids triggering MDI alerts)
Invoke-BloodHound -ExcludeDCs
# Good balance: Full data but avoids DC noise
Invoke-BloodHound -CollectionMethod All -ExcludeDCs
C:\AD\Tools\BloodHound-master\BloodHound-master\Collectors\SharpHound.exe --CollectionMethods All --ExcludeDCs
C:\AD\Tools\BloodHound-master\BloodHound-master\Collectors\SharpHound.exe --CollectionMethods All --ExcludeDCs --OutputDirectory "C:\Users\student544\Desktop" --OutputPrefix "bloodhound"
# SOAPHound bypasses traditional LDAP queries by talking to Active Directory Web Services (ADWS - Port 9389), mimicking legitimate AD Module traffic.
# 1. Build a local cache of domain objects (Reduces LDAP queries)
SOAPHound.exe --buildcache -c C:\AD\Tools\cache.txt
# 2. Generate BloodHound compatible JSON data
SOAPHound.exe -c C:\AD\Tools\cache.txt --bhdump -o C:\AD\Tools\bh-output --nolaps
bloodhound-python -u <user> -p <password> -d <domain> -ns <dc-ip> -c All
bloodhound-python -u <user> -p <password> -d <domain> -ns <dc-ip> -c All --zip
OPSEC
- Use
-Stealthto reduce noise — collects only session data. - Use
-ExcludeDCsto avoid triggering Microsoft Defender for Identity (MDI). - Prefer
bloodhound-pythonfrom Linux to avoid touching disk on the target.
Tips
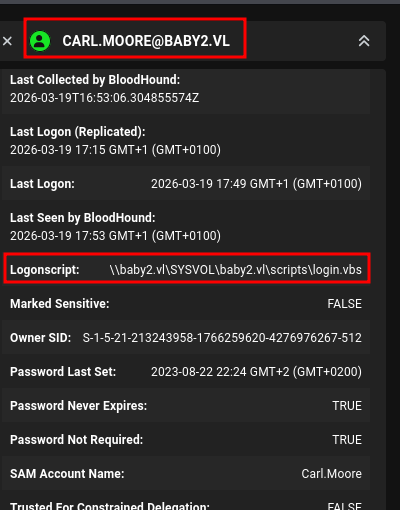
It's worth checking user properties in BloodHound — Logonscript paths can reveal interesting abuse opportunities.